Effective cyber reports require less tech talk
Reprints
The key to communicating effectively with company boards of directors on cyber risk is to discuss issues in business terms board members can understand and avoid overly technical language, experts say.
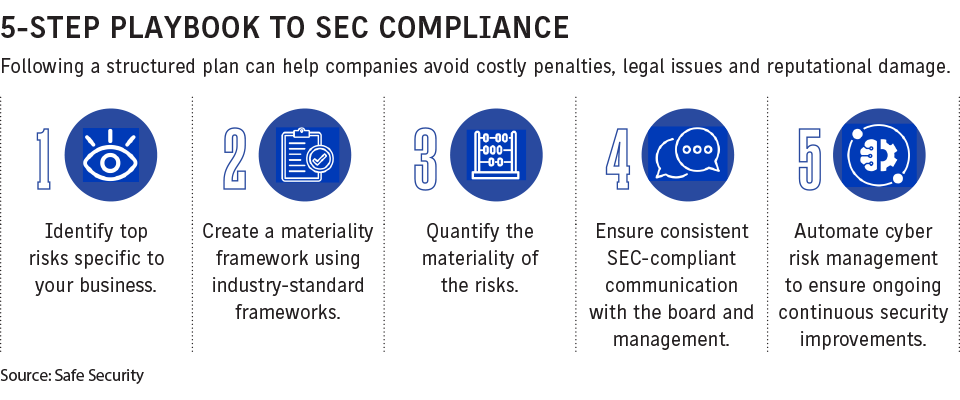
The issue is particularly significant in light of the cybersecurity rules issued by the U.S. Securities and Exchange Commission that takes effect Dec. 18, which requires public companies to determine an incident’s materiality and report it within four business days (see related story).
“If you don’t have that united front” and a cybersecurity plan in place, “the SEC rules should be forcing the issue,” said Tim Fletcher, Los Angeles-based CEO of Aon PLC’s financial services group in the United States.
At this point, relatively few board directors are knowledgeable about cyber risks, although progress is being made, experts say.
Part of the challenge is that cyber is a relatively nascent industry, said Mike Lefebvre, director of cybersecurity at SEI Sphere, an Oaks, Pennsylvania-based cybersecurity and information technology company, adding the issue is only about two-and-a-half decades old.
Its complexity means cyber risk “doesn’t translate well to boards” because they are looking at the issue from the “30,000-foot level,” said David Anderson, New York-based vice president of cyber for Woodruff Sawyer & Co.
If you “can align your message with what they’re thinking about,” such as what must be disclosed to the SEC and shareholders, it will be more effective, he said.
Risk managers and chief information security officers are responsible for keeping up to speed on cybersecurity, while the role of boards is to look at the issue within a broader context, doing what they can to ensure the proper protocols are in place when a cyber incident occurs, said Tara Bodden, general counsel, head of claims, at insurtech managing general agency At-Bay Inc. in San Francisco.
Boards need to be informed that cybersecurity is “not a technical issue but a business issue,” said Bhavesh Vadhani, Tysons, Virginia-based cybersecurity, technology risk and privacy practice global leader for CohnReznick LLP, an accounting, tax and advisory firm.
Right off, there is a language barrier, said Wade Chmielinski, Johnston, Rhode Island-based staff vice president and group manager cyber consultants at FM Global.
It is a challenge to introduce a complicated topic in simple terms the board can understand, as the wide array of systems and defenses involved can be very complicated, said Kevin Neslage, Miami-based U.S. incident response claims counsel for Resilience Cyber Insurance Solutions LLC.
“It’s really hard, sometimes, to convey technical concepts without getting too technical,” Mr. Chmielinski said. Reports to the board should be “in simple, understandable terms for everyone in the room” regardless of their expertise.
“There should be some kind of a translation of CISO-speak to a language that the board can truly understand. When it comes to cyber risk, you can get really tied up in jargon,” said John Farley, New York-based managing director of Arthur J. Gallagher & Co.’s cyber liability practice.
Boards do not have to know the type of chips the company uses, said Thomas O. Gorman, a partner at Dorsey & Whitney LLP in Washington. Everyone can understand the risks if they are told the company has 5 million customers, stores personal data and has a seven-year-old system, he said.
“You can’t just spout off and sound like a security guy,” Mr. Chmielewski said. “You have to be able to turn it into a conversation they can understand,” pointing out how gaps in security can result in loss “and then quantify that.”
Mr. Anderson stressed the importance of being quick, saying the board will lose interest if “you’re not delivering a clear and concise message” in 15 to 20 minutes.
“Communication is fundamentally the most important element of relationships between risk managers and boards, and it’s incumbent upon risk managers to keep the message tight,” he said.
Mr. Chmielinski said FM Global has found that “the more seasoned the person delivering the information, the more efficient way we can deliver it,” which avoids “going down rabbit holes.”
“We do a lot of work to make sure we can summarize and target those areas that are most critical, that are going to have the most impact,” he said.
Alexander H. Southwell, a partner with Gibson Dunn & Crutcher LLP in New York, who co-chairs the firm’s privacy, cybersecurity and data innovation practice group, said there should be regular conversations with the board.
“It’s hard to talk about incidents when you’ve never had those conversations with the board before,” he said. “If there is a history and common language around cyber risk it can help make conversations go more smoothly” if an incident occurs.
Mr. Chmielinski said that on some occasions, there may be pressure from non-board company employees to “soften” the information presented, “and that becomes a challenge,” he said, adding, “We think transparency is the best remedy.”
The cyber expert is underrepresented overall in the boardroom today, although boards are seeking this expertise, said Pankaj Goyal, chief operating officer of Palo Alto, California-based cybersecurity company Safe Security.
“I would imagine that the majority of board members do not today have extensive experience in cybersecurity,” and many of them are learning about it quickly, Mr. Farley said.
Mr. Southwell noted the SEC considered requiring that boards disclose which directors have cyber expertise. While that measure did not make it into the final rule, boards now often seek directors with this expertise, he said.
It is no different from when companies responded to the Sarbanes-Oxley Act of 2002, which required directors to have financial expertise, Mr. Lefebvre said.
“We may be on the cusp” of addressing this issue for cyber, although it is not expected to be resolved overnight, he said.
“I think we’re on the right path and closer to an ideal situation than we would have been a few years back,” Mr. Anderson said.