Drive for smart fleets collides with cyber risk
Reprints
The growing cyber sophistication of trucks and automobiles is increasing the cybersecurity risks of trucking companies and other fleet operators.
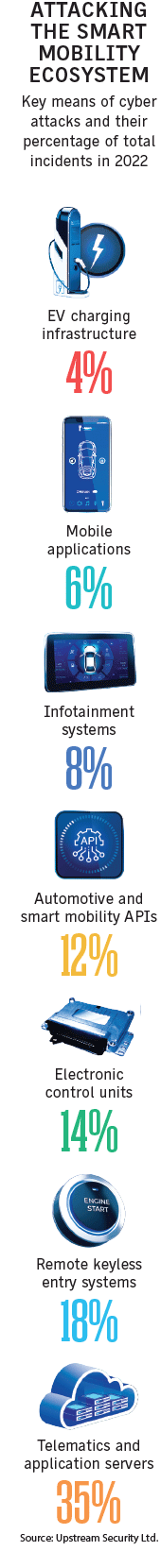
Modern vehicles contain about 100 million lines of code, according to widely cited industry data, and their potential vulnerabilities include telematics and application servers, remote keyless entry systems, electronic control units, application interfaces, infotainment systems and mobile applications.
And the amount of code will only increase as more vehicles move more toward becoming autonomous, experts say.
All this creates significant cybersecurity and related privacy concerns that must be addressed by manufacturers, fleet operators and other trucking companies, logistics companies and, ultimately, insurers, they say.
While there have been relatively few cyber-related incidents to date — many of them instigated by so-called “white hat” researchers — experts say the frequency will certainly increase as more cybercriminals pay attention to the segment.
Meanwhile, trucking and car fleets must also contend with the ransomware and phishing risks plaguing many other industries.
Government agencies addressing the issue include the U.S. Department of Transportation’s National Highway Safety Administration, which issued updated cybersecurity best practices guidance last year, and the National institute of Standards and Technology.
U.S. Rep. Bob Latta, an Ohio Republican, has proposed the Self-Drive Act, which would require manufacturers of “highly automated vehicles” to develop a written cybersecurity policy. He has unsuccessfully sought passage of the bill in the past but is expected to reintroduce it this year.
In 2021, the International Organization for Standardization introduced standards that specify cybersecurity risk management engineering requirements for road vehicles’ electrical and electronic systems, including their components and interfaces.
Major vehicle manufacturers are aware of, and responding to, cybersecurity issues, experts say, but they point out that even if they successfully address concerns with new vehicles, many unenhanced, older vehicles remain on the road.
Many observers point to a 2015 case in which researchers remotely hacked a Jeep Cherokee, slowing it to a crawl on a highway, which led to Chrysler Corp.’s recalling 1.4 million vehicles.
“That was eight years ago and think about how much the technology has changed since,” said Gwenn Cujdik, Exton, Pennsylvania-based manager of the cyber incident response team at Axa XL, a unit of Axa SA.
Experts also note an apparent prank in Russia in September in which dozens of cabs converged on a single address in central Moscow, causing a major traffic jam.
Among other incidents, last year a 19-year-old security researcher described in a blog how he took advantage of a bug to remotely hack into more than 25 Teslas — “By accident. And curiosity.”
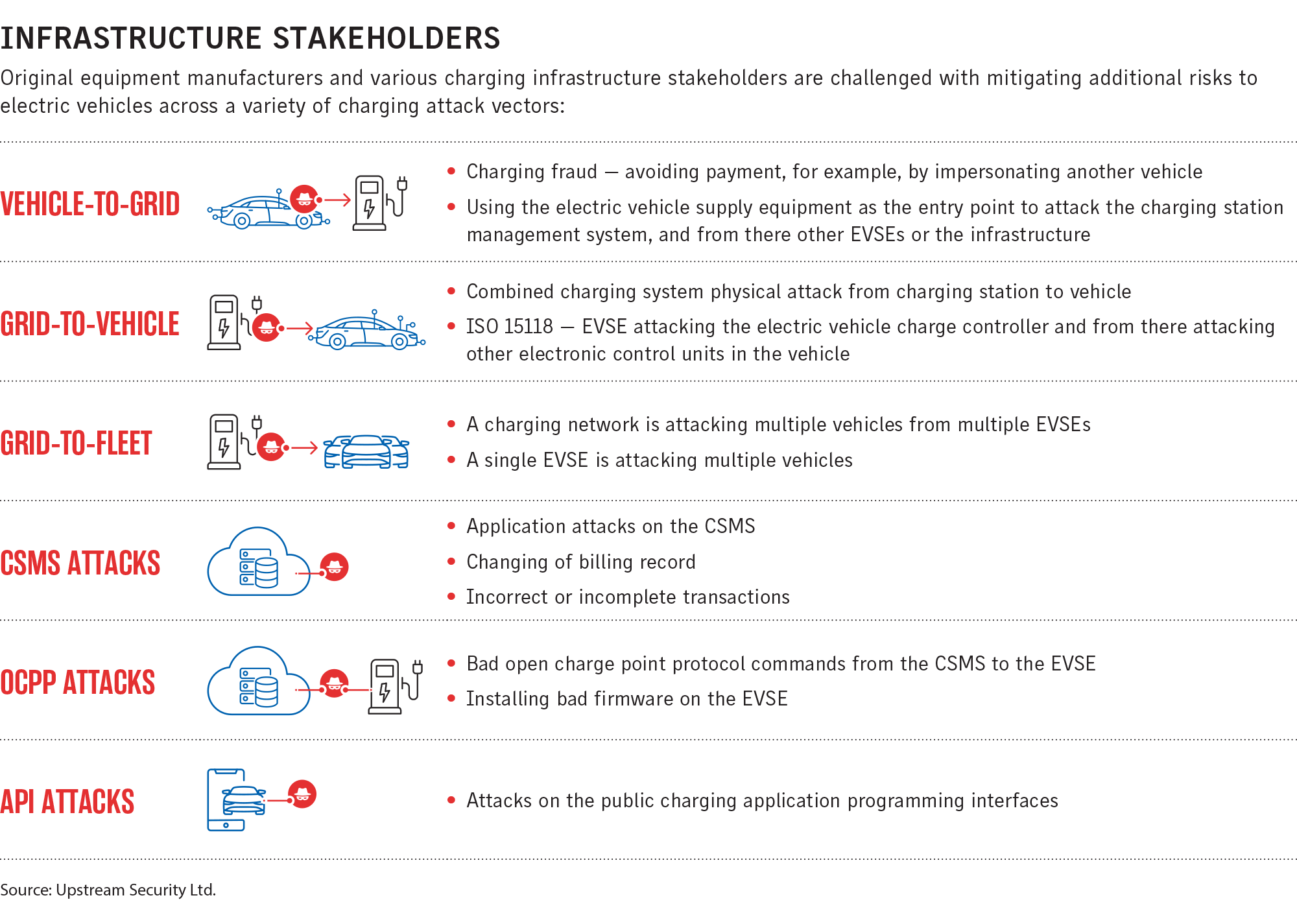
New technologies are beginning to leverage advanced connectivity, including “vehicle-to-vehicle,” “vehicle-to-infrastructure,” “vehicle-to-pedestrian,” “vehicle-to-grid” and “vehicle-to-everything,” according to the 2023 Global Automotive Cybersecurity Report by Herzliya, Israel-based Upstream Security Ltd., whose funders include auto manufacturers and insurers (see illustration).
Upstream tallied 268 automotive and smart mobility cybersecurity incidents in 2022.
The “attack surface” is growing exponentially, increasing attackers’ ability to gain access, said Brent Rieth, Chicago-based U.S. practice leader, E&O/cyber broking, at Aon PLC.
“When you think of all that can go wrong” it is “pretty substantial,” said Scott Swanson, Chicago-based practice leader, security advisory, at Aon.
Jacob Petty, Los Angeles-based senior vice president and Southwest team leader FINEX E&O/cyber practice at Willis Towers Watson PLC, said the biggest issue is cyber liability business interruption, as fleet operators take advantage of new technology to cut costs. However, this puts them at risk of hacking and ransomware attacks, he said.
As new technologies are introduced, they will require “another level of cybersecurity to be put in place,” for which the automotive industry will be held responsible, said Michael Stankard, Detroit-based managing director, industrial & materials & automotive practice at Aon.
Ideally, telematics — vehicle onboard communication services and applications that are used to track vehicle performance and driver behavior, among other things — only give access to authorized sources, “but not all telematic devices are created equal or are of the same quality,” said Ben Gardiner, senior cybersecurity research engineer with the Alexandria, Virginia-based National Motor Freight Traffic Association.
Adoption of cybersecurity measures varies widely. In trucking, the spectrum goes from companies with highly developed software development resources that are buying better equipment and reconfiguring their telematics deployment to reduce risks, down to companies with one or two trucks, Mr. Gardiner said.
Most attacks to date have been by academic researchers, who are investigating the challenges of the technologies and have no malicious intent, said Dennis Kengo Oka, Tokyo-based senior principal automotive security strategist and executive adviser at Synopsys Inc., who has written a book on the subject. They are finding security vulnerabilities and alerting car manufacturers, he said.
But Mr. Oka said he’s seeing a gradual shift, with actual crimes being committed, including thefts tied to keyless entries.
Mr. Oka said that while there is an inadequate return for a cybercriminal to attack a single vehicle, that will no longer be true “as we move toward fleet management systems.”
Despite the threats, the transportation industry as a whole has “not constructively invested in technology or utilized third-party vendors to supplement their knowledge of technology,” said Nadia Hoyte, New York-based national practice leader, cyber, with USI Insurance Services LLC.
Much of the focus so far has been on logistics and the threat of a cyber incident shutting down the flow of products, said Axa XL’s Ms. Cujdik.
John Bambenek, Mahomet, Illinois-based principal threat hunter at Netenrich Inc., a cloud data analytics platform, said fleet management systems are vulnerable to the same supply chain risks that cybercriminals took advantage of to shut down Colonial Pipeline Co. in May 2021, leading to gas shortages in some parts of the United States.
“If you manage to disrupt the ability of depots to get gas to gas stations, by disrupting tractor trucks,” it could create supply chain issues that could have a significant impact, he said.
There will be more attacks against supply chains because criminals realize they can be lucrative, Ms. Hoyte said. “In the future, the supply chain issue is going to raise its head in a very, very ugly way,” she said.
Driverless trucks may be transporting goods across the country in the not-too-distant future, said John Farley, New York-based managing director of Arthur J. Gallagher & Co.’s cyber liability practice. If that happens, there will be a great reliance on GPS systems, and if those fail or are compromised, “one could see deliveries coming to a screeching halt,” he said.
There are also significant privacy risks.
“The automotive industry has rapidly adopted technology on a very wide scale,” and vehicles are collecting “more information on individuals than they ever have before,” Mr. Farley said.
Technology may also move toward cars being started with fingerprint identification, much like cell phones. “There’s a whole element of privacy liability that comes with today’s modern cars,” Mr. Farley said.