War exclusion gains traction in cyber market
Reprints
A requirement by Lloyd’s of London that standalone cyber policies include exclusions for state-backed cyberattacks, beginning next March, will provide some clarity to insurers and policyholders, but significant areas of ambiguity remain.
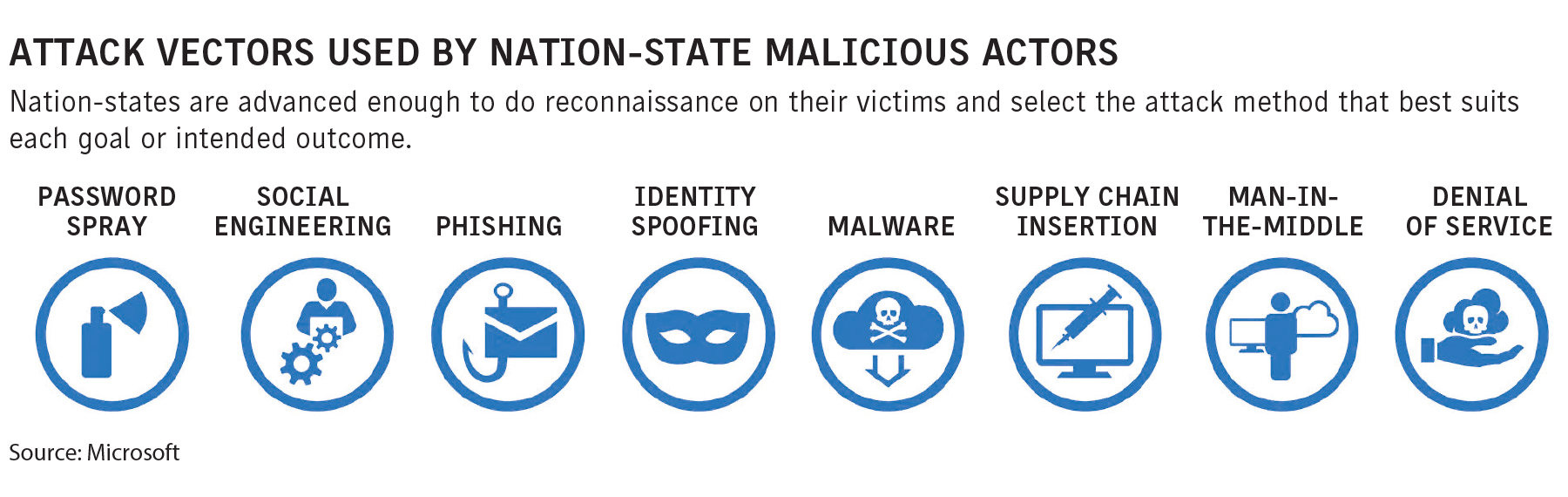
Many observers say the question of when cyberattacks can be attributed to nation-states is inconclusive and may ultimately be resolved only after years of litigation (see related story).
They say also that the exclusion comes against the backdrop of a hard cyber market and its ultimate effect on rates is unclear.
According to the Center for Strategic & International Studies, a Washington-based think tank that keeps a running tally of cyberattacks on government agencies, and defense and high-tech companies, or economic crimes with losses of more than $1 million, there were 96 attacks this year through September, with many cited as nation-state-related.
The Lloyd’s Market Association in November 2021 introduced four model clauses designed to exclude coverage for war risks from cyber policies.
Lloyd’s said in an Aug. 16 market bulletin that while it remains “strongly supportive” of writing cyberattack cover, “if not managed properly it has the potential to expose the market to systemic risk that syndicates could struggle to manage,” with losses potentially exceeding the market’s ability to absorb.
Experts say the ongoing Russia-Ukraine conflict is lending urgency to the issue. Many point to the litigation that stemmed from the 2017 NotPetya ransomware attack, which was instigated by Russia against Ukraine.
The New Jersey Superior Court in Elizabeth ruled Jan. 13 in Merck & Co.’s favor in litigation filed against a Chubb Ltd. unit in which the pharmaceutical company sought coverage for damages sustained in the NotPetya attack, according to the ruling in Merck & Co. v. ACE American Insurance Co.
Other insurers have revised their war exclusions as well, including Chubb Ltd., Beazley PLC and Crum & Forster, experts say. The Lloyd’s rule applies most directly to large corporations that go through its market.
Paul Bantick, global head of cyber risks at Beazley, which introduced an exclusion compatible with Lloyd’s on Oct. 1, said that in both cases, “it’s not necessarily about restricting cover” but providing clarity and excluding war from cyber coverages just as it is already excluded from other policies. “It’s bringing cyber language into the modern world,” he said.
Roman Itskovich, San Francisco-based chief risk officer and co-founder of insurtech managing general agency At-Bay Inc., said the Lloyd’s wording is “a pretty effective exclusion” that does not ask for a declaration of war and gives insurers the capability of deciding if it applies if governments are slow to declare war.
The exclusions have their detractors.
“I frankly disagree with the concept of excluding nation-state attacks against private enterprises,” said Dan Burke, San Francisco-based national cyber practice leader for Woodruff Sawyer & Co.
Policyholders have had two years of significant rate increases, and now insurers are starting to pull back coverage, Mr. Burke said. “It’s a slippery slope, taking away a lot of the value of the insurance policy,” he said.
Many say attributing disruptions to nation-state attacks is a difficult challenge.
“That is going to be tough to achieve,” as various criminal groups disappear, regroup, rebrand or break off into smaller subsets, said Mark Lance, Richmond, Virginia-based senior director, cyber defense, at GuidePoint Security LLC.
Parties are being asked to prove who conducted the cyberattack “and that’s really hard,” said Peter A. Halprin, a partner with Pasich LLP in New York. “It’s a very, very complicated issue,” he said.
“It really will come down to parsing what language was actually put into the policy,” how it applies, and whether the cyberattack coincided with a physical attack, said Scott Godes, a partner with Barnes & Thornburg LLP in Washington. It calls for an “old-fashioned look” at what the insurer is asserting and how it applies to the circumstances presented, he said.
The Lloyd’s exclusion “makes the most noise” because of its large size and the number of participants, said Kyle Bryant, New York-based managing director and chief underwriting officer international for Resilience Cyber Insurance Solutions. “I do see some (other) carriers beginning to use their versions to test the market,” he said.
Crum & Forster changed its war exclusion language to make it clearer about a year ago, and by and large it has not emerged as a major issue, said Nick Economidis, Houston-based senior vice president of cyber for the insurer.
Some see more insurers doing the same.
“You’re seeing non-Lloyd’s carriers taking a closer look at their own war exclusions to see if they’re in line with what Lloyd’s is proposing, as well as seeing a tightening industrywide of the war exclusion and much more focus on those exclusions,” said Jes Alexander, senior research analyst, professional lines, for the International Risk Management Institute Inc. in Dallas.
However, Samantha Levine, Denver-based senior vice president, professional and cyber solutions, at CAC Specialty, an affiliate of brokerage Cobbs Allen, said that if no material impact or large incident emerges from the Ukraine war, “I could see some U.S. markets striving to maintain a leg up” from a competitive perspective by not making changes to their policies’ war exclusions. “A lot of factors determine whether everyone does it,” she said.
Experts predict the Lloyd’s war exclusion will evolve further.
“I foresee that we will see additional changes coming,” said Shannon Fort, London-based partner in McGill & Partners financial lines division.
The situation will continue to change, not just the policy wording but the political landscape and the nature of cyber warfare, said Michael S. Levine, a partner with Hunton Andrews Kurth LLP in Washington. “It’s all evolving at such a rapid pace that the policy wording is going to have to evolve as well to keep up with it.”