High-stakes cyber claims demand quick action
Reprints
The biggest difference between handling cyber claims and more traditional property/casualty claims is the speed with which the process unfolds, which demands an immediate, coordinated response by the policyholder, insurer and broker, observers say.
Claims handling for the more traditional property/casualty lines is a comparatively leisurely process, in which a claim is made, the policyholder awaits a decision on coverage, and matters progress from there to either a paid claim or litigation, they say.
In contrast, cyber claims are characterized by often frantic speed, with simultaneous events occurring on multiple fronts and conceivably the company’s existence at stake.
“Every cyber incident is an emergency situation,” said Kristine D’Amato, New York-based national claims counsel, executive and professional risk solutions, for USI Insurance Services LLC.
“You have a policyholder facing something it has never faced before” who “oftentimes feels they don’t know exactly what’s happened,” she said, adding that every minute can cost companies if their operations are shut down.
John Scordo, New York-based cyber claims advocacy leader for Marsh LLC, said the broker is already collaborating with insurance adjusters “literally the first hour” after a ransomware event.
“There are multiple parties that have to be involved; schedules have to mesh for at least the first 48 hours,” said Dan Twersky, New York-based global cyber claims leader for Willis Towers Watson PLC. He noted that cyber events often happen on a Sunday, when it can be difficult to reach people.
The critical nature of the situations adds to the sense of urgency, observers say.
Cyber events “can really bring down the company,” with some businesses finding that hackers have made their source code publicly accessible, said Christine Flammer, New York-based claims manager for Axa XL, a unit of Axa SA.
Threats are constantly evolving, even on a daily basis, as hackers find new ways to infiltrate networks, said Savanna Boyles, New York-based senior director of claims for insurtech Corvus Insurance Holdings Inc. “We see new twists and iterations in the types of claims on a continuous basis,” she said.
Another issue is determining the extent of cyber losses.
Initially, everyone “is trying to figure out what actually happened,” whether it is a breach, a ransomware incident “or some other variation,” said Daniel J. Healy, a partner with Anderson Kill P.C. in Washington. Determining the extent that data is compromised and what has been damaged “can be pretty complicated,” he said.
Ms. Boyles said that unlike fire damage, where the evidence of loss is tangible, cyber losses are “far more elusive in measurability, and the extent and the cost of the loss isn’t always as cut and dried as it is with other lines.”
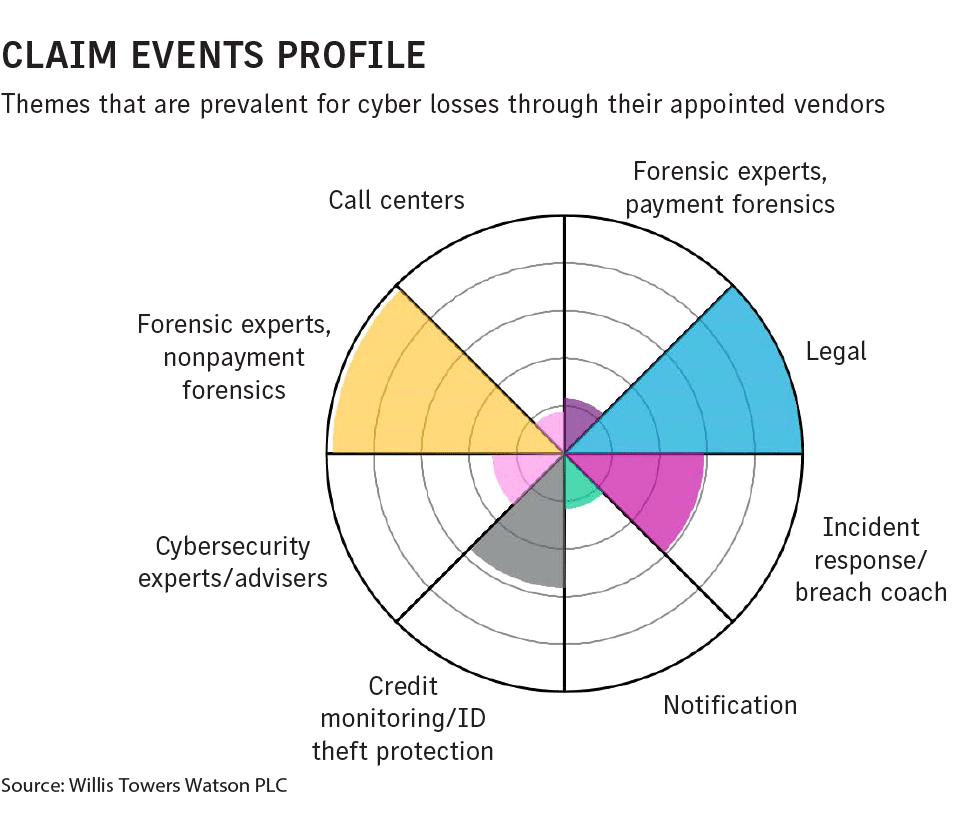
Another issue with cyber claims is the number of parties involved, including lawyers, forensics experts, security and public relations specialists, which requires insurers to act as quarterback, said Tim Zeilman, Simsbury, Connecticut-based global cyber product owner at Hartford Steam Boiler Inspection and Insurance Co., a Munich Reinsurance Co. unit.
Despite insurers’ immediate initial involvement, because so many “coverage buckets” are involved, “the claims continue for a long time” and can involve first-party, business interruption, regulatory, class-action, fraud and crime claims, Mr. Scordo said.
Furthermore, cyber claims may include many exclusions that need to be understood and could raise so-called silent cyber issues, said Jamie Taylor, London-based senior management director in data protection & cyber security at DWF Group, a provider of legal and business services.
Thomas H. Bentz, a partner with Holland & Knight LLP in Washington, said, the “burn rate,” how quickly the claims exceed retentions, is significant with cyber.
In a typical directors and officers class action, he said, it takes “months, if not years,” before claims pierce retentions and policy limits. With a cyber claim, it may happen the first day, he said.
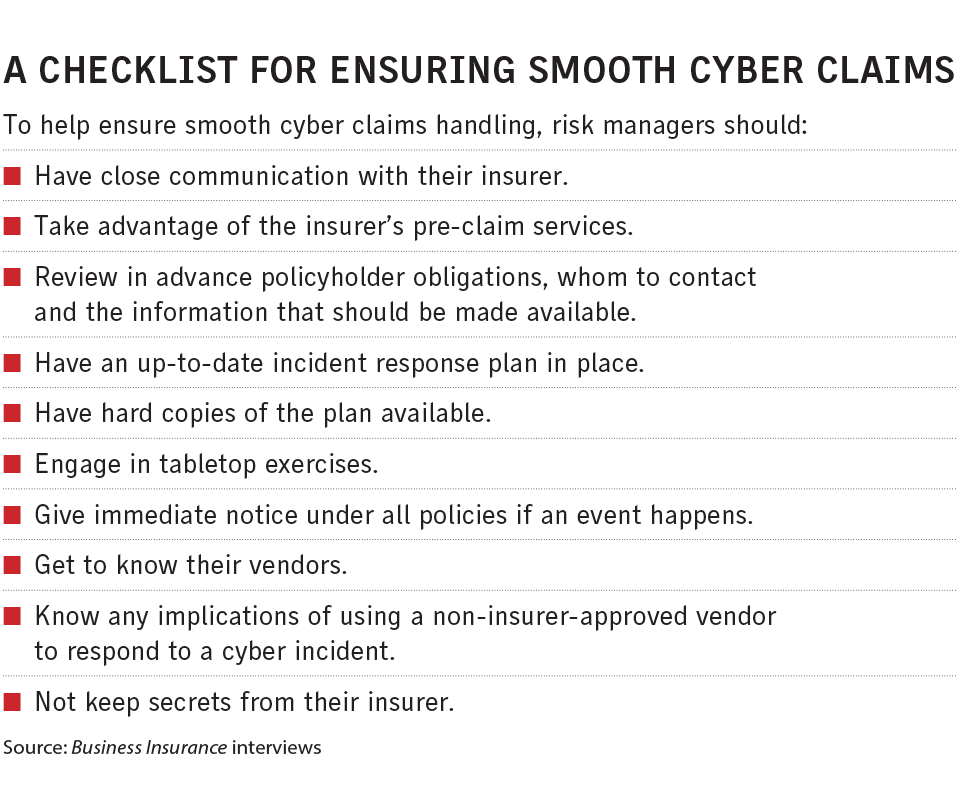
The situation also demands advance preparation, said Katherine Keefe, Marsh’s Philadelphia-based cyber incident management leader for the U.S. and Canada. She said Marsh spends much time with policyholders before they’re ever faced with a cyber incident to familiarize them with their policy and their options, so they’re prepared to use available resources “to the maximum effect.”
An often-mentioned problem is when policyholders use vendors that are not approved by their insurer to respond to a cyber incident.
Ms. Boyles said that sometimes in the heat of the moment policyholders, who are unaware their insurers have a 24/7, 365-day response team, “just kind of panic and perhaps try to take matters into their own hands” and reach out to nonapproved vendors.
“It can become a major point” if that vendor cannot handle more complex matters such as a ransomware attack, she said.
Ms. D’Amato said, “There are policy forms that’ll allow some leeway of choice of vendor or counsel,” but almost invariably with the caveat that the insurer must approve the selection in writing.
“I have seen some policies that actually will say you don’t have to use a preapproved vendor, but if you don’t” there are different limits or retentions, said Joni Mason, New York-based senior vice president, national claims practice leader, at USI.
“My recommendation is to keep the carrier informed at every step” because it is more difficult to get insurers’ approval if the outside vendor has already been hired, Ms. D’Amato said.
Cyber experts stress the need to immediately inform the insurer of the claim.
“There’s nothing worse than having to adjust a cyber claim in hindsight. … You’re just sitting there, trying to unpick decisions made in the heat of the moment,” said Roger Francis, cyber claims director at CFC Underwriting Ltd. in London.
“Many times, when people don’t report initially, it can become a greater problem down the road, and if there’s a threat actor in the system, it gives them more time to move around and possibly deploy malware,” said Lisa Jaffee, New York-based assistant vice president of cyber/tech/media/crime claims for Hiscox USA.
Another issue that may arise is a lack of cooperation on the policyholder side.
Tara Bodden, general counsel and head of claims at insurtech At-Bay Inc. in San Francisco, said it can be challenging to track down a claim’s cause if employees “kind of get in the way” on the investigation because they’re worried about being blamed and losing their jobs.
Experts say policyholders should be aware that checking to make sure in ransomware situations that the hacker is not on the list of sanctioned entities of the U.S. Department of the Treasury’s Office of Foreign Assets Control can add time to the process.
An October 2020 advisory from the department warns that companies, including cyber insurers, that facilitate ransomware payments to sanctioned entities may be violating OFAC regulations.
“It certainly is a challenge to make sure that you’re complying with all the appropriate laws and regulations, particularly OFAC’s,” Mr. Zeilman said.
“It’s something that adds another kind of level of complexity to claims handling” that runs parallel to the effort of working with policyholders and seeing they are properly reimbursed, he said.
Policyholders, insurers must be in step on claims
Good communication between policyholders and insurers is critical to successful cyber claims handling, experts say.
Make sure “that you’re communicating with the claims handler,” including any claims updates, said Joni Mason, New York-based senior vice president, national claims practice leader, for USI Insurance Services LLC.
“Policyholders should prepare long before a claim even happens,” said Savanna Boyles, New York-based senior director of claims for insurtech Corvus Insurance Holdings Inc.
“You’re really behind the 8-ball if you wait for the day IT says they see something funny in your network.”
Many cyber insurers offer pre-claim services to better prepare companies for an event, including providing a free hour’s consultation with an attorney to ask any questions, said Stuart Panensky, a partner with FisherBroyles LLP in Princeton, New Jersey.
Companies should also do tabletop exercises, which is a great way for a policyholder to learn what to do before an incident occurs, he said.
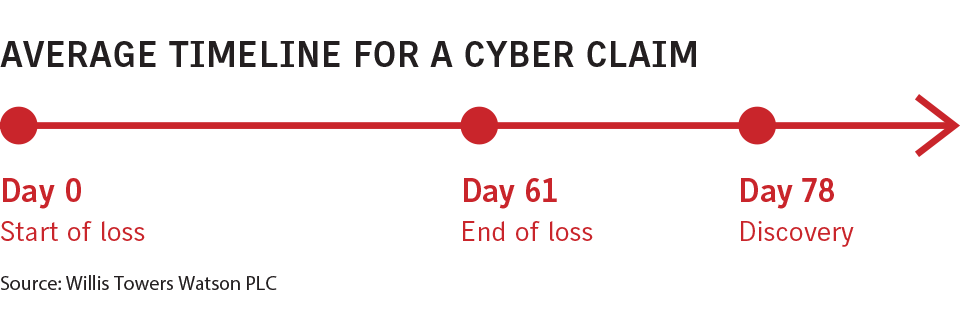
Policyholders are going “even outside their standard tabletop exercises” to review in advance their obligations, whom they should contact, what information should be available if an event occurs, and what they should be tracking insofar as losses and the additional expense being accrued, said Dan Twersky, New York-based global cyber claims leader for Willis Towers Watson PLC.
Preparation should include having hard copies of incident response plans in case there is no access to online copies, Mr. Panensky said.
Policyholders should also know the implications if they use a non-approved vendor in their response to a cyber incident and be open with their insurers, experts say.
“Don’t keep secrets,” Mr. Panensky said. Even if there is a coverage issue, insurers “will pay for everything” they have contracted to pay, he said.
Cyber incident victims should also give notice immediately under all policies, “not just cyber policies,” said Daniel J. Healy, a partner with Anderson Kill P.C. in Washington.
Complex cyber claims test insurers’ technical expertise, capabilities
Many experts say cyber liability insurers have done a good job overall in handling claims, but their expertise and efficiency vary and it can sometimes take months for claims to be paid.
“Cyber insurance has really evolved over the past decade,” said Savanna Boyles, New York-based senior director of claims for insurtech Corvus Insurance Holdings Inc.
“The nuances of cyber insurance and cyber claims were not fully understood” a decade ago, but programs have since matured, as insurers have added technical expertise, she said.
John Scordo, New York-based cyber claims advocacy leader for Marsh LLC, said, “The nature of the cyber event and claims and the interaction with the insurer is really very intertwined, and I think carriers are doing a really good job” in their advice and responsiveness.
Christine Flammer, New York-based claims manager for Axa XL, a unit of Axa SA, said insurers are doing well not only in handling claims in the heat of the incident but in partnering beforehand and debriefing afterward as to what can be done better the next time.
Roger Francis, cyber claims director at CFC Underwriting Ltd. in London, said of insurers, “The ones that are handling it best are spending time and money to hire talented individuals with the right expertise.”
Some insurers “tend to drag their feet a little bit” and scrutinize losses more closely as the market has hardened, said Dan Burke, San Francisco-based national cyber practice leader for Woodruff Sawyer & Co.
“We’ve had more trouble with insurers who are starting to outsource a lot of the process,” said Dan Twersky, New York-based global cyber claims leader for Willis Towers Watson PLC.
“They’re coming back and asking a lot of questions before paying,” sometimes months later, he said.
Mr. Twersky said there’s sometimes “Monday morning quarterbacking” about the period when people were scrambling to respond to a cyber incident, which makes it difficult for the policyholder.
Mr. Twersky said the pandemic has complicated matters, as claims adjusters have not been able to “go down the hall and speak to their manager.”
Read Next
-

Insurers mobilize to identify comp fraud in effort to stem rise in suspicious claims
Fraud investigations are triggered by red flags in a workers compensation claim, and the examples run the gamut.