Cyber threats escalate with global exposure
Reprints
The threat posed by nation states’ infiltration into the United States’ critical infrastructure is growing, and the federal government and private companies must do more to address the risk, experts say.
While the Biden administration has made a strong push toward helping companies with the issue, much remains to be done, they say. Meanwhile, private sector efforts to address the issue have been uneven.
Complicating the problem, boundaries between nation states and cybercriminal gangs operating within them are often permeable, with criminals sometimes operating with their governments’ knowledge and even at their behest, experts say.
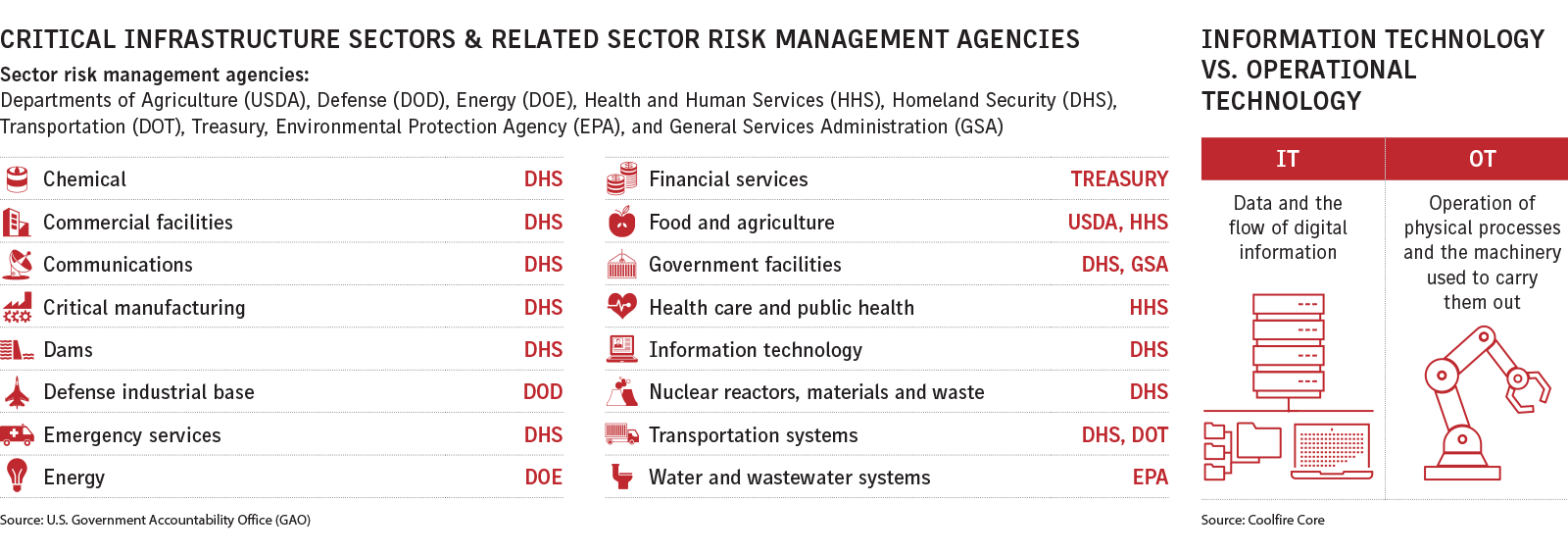
The Gaithersburg, Maryland-based National Institute of Standards and Technology, which has issued guidance on addressing cyber threats, has outlined 16 critical infrastructure sectors, including the defense industry, energy, food and agriculture, and health care. It also recommends steps companies can take to improve their cyber hygiene (see related story).
Meanwhile, in light of a recent New Jersey court decision, insurers may be reconsidering the traditional war clause exemption in their non-cyber policies (see related story).
Nation states are the “greatest threat that’s posed to the U.S. right now as a nation. I think we’re ill-prepared,” said Ted Theisen, Washington-based senior managing director at Ankura Consulting Group LLC and a former special agent with the FBI, where he focused on cyber-related matters.
“As geopolitical tensions increase, you should expect an increase in cybersecurity threats, particularly against infrastructure and particularly against iconic U.S. and western brands, and the threat is real and escalating,” said Michael Bahar, a partner with Eversheds Sutherland LLP in Washington, who is a former U.S. House Intelligence Committee staff member.
“Certain countries have spent years and years mapping out our infrastructure and finding the weakest links, as well as the links that have multiplier effects,” he said, adding that so far there has been little direct activity.
Russia, China, Iran and North Korea are frequently cited by experts as targeting the U.S. infrastructure.
Experts say the Biden administration has made significant progress in addressing the issue, though some see room for improvement.
Mike McNerney, senior vice president of security for cyber insurer Resilience Cyber Insurance Solutions, in San Francisco, said, “This is the most aggressive administration when it comes to cyber security that I’ve ever seen.”
The Cybersecurity and Infrastructure Security Agency, part of the Department of Homeland Security, in particular, is taking a “very active role reaching out to the private sector,” he said.
However, “the federal government acts most of the time as a regulator,” and “is always going to be reactive,” said John Bambanek, principal threat researcher at San Jose, California-based Netenrich Inc., an information technology service management company.
“What is needed is better collaboration and more open conversations” between the government and the private sector, he said.
There are “too many regulators chasing too many regulations, each with their own kind of fine-tuning,” said Scott Corzine, Arlington, Virginia-based senior managing director at B. Riley Financial Advisory Services.
The government should move to a unified approach to protecting critical infrastructure rather than the current “alphabet soup” of regulators, he said.
Experts say last year’s Colonial Pipeline hack by a Russia-linked cybercriminal group — in which the company was forced to shut down its entire network, the source of nearly half of the East Coast’s fuel supply — was a wake-up call to companies about the risks they face.
And although it is believed the threat came from an insider, last year’s thwarted attempt to remotely put lye into Oldsmar, Florida’s water treatment facility has served as a warning as well.
William Altman, principal cybersecurity consultant with San Francisco-based CyberCube Analytics Inc., said the U.S. critical infrastructure is not monolithic but rather “a patchwork of different technology and security measures.”
Larger organizations that have invested heavily in cybersecurity have done a reasonable job in putting necessary controls in place, said Jason Rebholz, chief information security officer at Corvus Insurance Holdings Inc. But other entities, such as smaller municipalities, often don’t invest heavily in cybersecurity and are inadequately protected, he said.
“One of the key challenges for companies is to recognize that almost every company at this point is a potential target,” said Joshua Larocca, New York-based senior managing director at Stroz Friedberg, an Aon PLC unit.
CLICK IMAGE TO ENLARGE
Security efforts in private industry often focus on information technology at the expense of operational technology, which refers to the hardware and software that operates physical processes, including power plants, oil rigs and manufacturing assembly lines.
Rotem Iram, co-founder and CEO of San Francisco-based insurtech At-Bay Inc., said that tackling cybersecurity risk requires “a lot of work” by both IT and engineering staff “to really make it a priority for the company.”
Engineers often mistakenly believe operational technology systems are safe from manipulation because there is an “air gap,” which means the systems are not connected directly or indirectly to the internet.
“Air gaps sometimes give you a false sense of security,” said Wade Chmielinski, staff vice president, cyber hazards, at Johnston, Rhode Island-based FM Global. “They’ll think they are air gapped, but all it takes is one device plugged into something that doesn’t necessarily need a wire” to change that.
Awareness of the issue is improving, Mr. Altman said.
Insurers have long seen nation states’ potential threat, and many are already excluding coverage. “I don’t really see that changing in the foreseeable future,” Mr. Rebholz said.
Market sources say Chubb Ltd. has changed its cyber policy language to address the issue of a nation-state event. A company spokesman declined to comment.
Last year, Lloyd’s Market Association introduced four new war, cyber war and limited cyber operations exclusions for standalone cyber insurance policies.
One exclusions states, for instance, “Notwithstanding any provision to the contrary in this insurance, this insurance does not cover any loss, damage, liability, cost or expense of any kind (together ‘loss’) directly or indirectly occasioned by, happening through or in consequence of war or a cyber operation.”
“I would hope we can be much more creative than just coming up with broader exclusionary language,” said Shannon Groeber, New York-based executive vice president of CFC Underwriting Ltd.
The cyber insurance market still has to “find ways to refine the coverage that they really intend to provide, and I think we’re still only halfway down the road,” said Christopher Keegan, New York-based head of the cyber liability practice at Beecher Carlson, a unit of Brown & Brown Inc.
Some underwriters are trying to develop wordings that will make clear whether a cyberattack by a nation state attack is covered.
But most attacks that have taken place have been covered by the cyber insurance market and attacks not related to physical war will likely continue to be covered, he said.
John Farley, New York-based managing director of Arthur J. Gallagher & Co.’s cyber liability practice, said, “We’ve always had some exclusionary language related to war or warlike actions in our policies, both in cyber and many other lines of coverage,” but the exclusions’ scope can be negotiated.
Read Next
-

Silent cyber ruling has insurers looking closer at war clause
A ruling issued by a New Jersey court that addresses the issue of “silent cyber,” where cyber coverage is not explicitly covered, is expected to be influential in changing the traditional war clause exclusion in non-cyber policies.