Cyber defense systems can foil ransomware
Reprints
Technical approaches to addressing ransomware’s threat are effective, but increasing employee awareness will also go far to address the problem, experts say.
Ransomware remains a major issue, with attacks totaling 495 million globally in the first nine months of 2021, up 148% from the year-earlier period, according to San Jose, California-based cybersecurity company SonicWall.
Its impact is compounded by the risk of double extortion, in which hackers encrypt a company’s data and also threaten to release the information publicly.
Companies that introduce security measures, including multifactor authentication, backups and incident response plans, are less likely to be seriously hit by a ransomware attack.
The majority of attacks can either be stopped or detected early enough so that they do not turn into a massive event, said Mark Sangster, Waterloo, Ontario-based senior vice president, industry security strategy, at eSentire Inc., a cybersecurity company.
Training employees to avoid clicking on malicious links is particularly critical with so many people working from home on systems that may be less secure than their company’s.
“They’ve got to be able to leverage sound judgment when evaluating the phone calls, the phishing emails, the malicious attachments they might receive in emails or other situations,” said C.J. Dietzman, Charlotte, North Carolina-based managing director and cybersecurity marketplace leader for Marsh LLC.
Employees should also be warned against using their work computers for personal business. If the third-party business gets hacked, “it’s easy to migrate over” to the business’ system, said Leann Nicolo, Denver-based incident response director for cyber insurance and security company Coalition Inc.
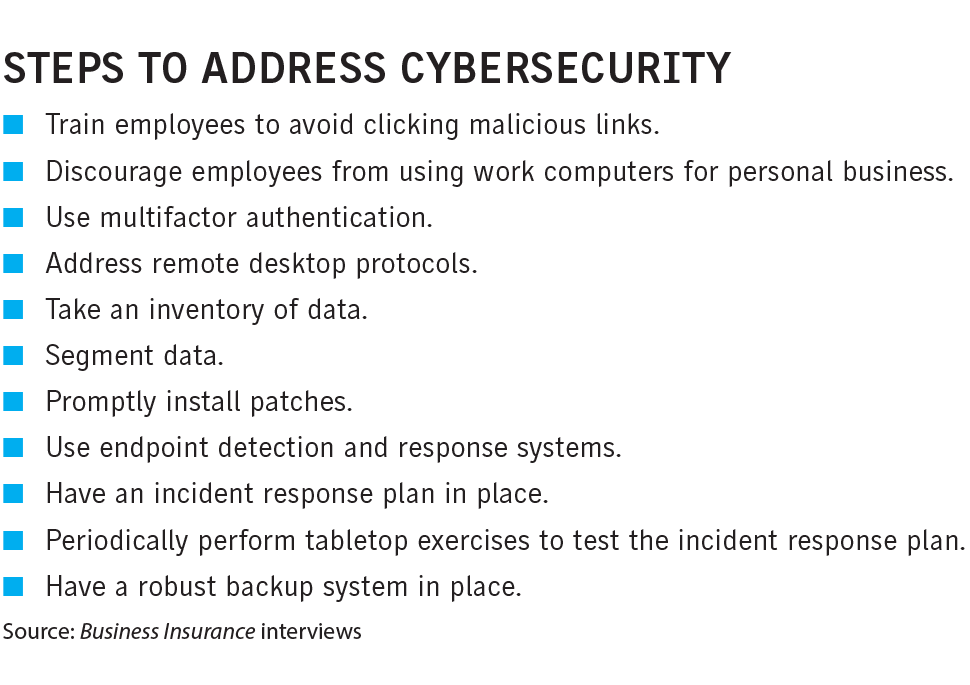
A critical factor in a successful cyber defense is multifactor authentication. While there are different types of MFA, examples include submitting a numeric code sent to a phone via text message in addition to a password to gain entry into a system.
MFAs are the least complicated cybersecurity measure to implement and have the highest return on investment, said Rajeev Gupta, co-founder and chief product officer at Pleasanton, California-based cyber insurer Cowbell Cyber Inc.
Experts say remote desktop protocols, a technical standard for using a desktop computer remotely that is often used by IT departments to troubleshoot, are often manipulated by hackers.
About half of all ransomware attacks start with RDPs, which are “incredibly easy to break into” and the equivalent of putting a sign on one’s lawn inviting the bad guys to come in, said Rotem Iram, co-founder and CEO of cyber risk specialist At-Bay, based in Mountain View, California.
RDPs “need to be locked down,” said Tom Finan, director, cyber practice, for Willis Towers Watson PLC in Washington.
An inventory of data is critical, experts say. “A lot of organizations don’t have a grasp even of what data they hold and where they hold it, ” said Shawn Melito, chief revenue officer of BreachQuest in Altoona, Pennsylvania. This can include sensitive data such as personal identifiable information.
Access to data should also be segmented. For example, there’s no reason why someone in operations needs to have access to financial data, Mr. Melito said, adding that data should not be kept indefinitely.
Mr. Sangster said companies should practice “privilege access management,” which incorporates the principle of “least privilege” by limiting system access to the minimum level needed. “If you don’t need access to specific controls, to specific data bases or files, by default you shouldn’t have them,” he said.
It’s also important to install patches promptly.
Jonathan Rajewski, South Burlington, Vermont-based managing director at Storz Friedberg, an Aon company, said he has seen cases in which patches were still not installed 30 to 45 days after they became available.
Companies should also have an endpoint detection and response system in place. This involves combining continuous monitoring and data collection, with an immediate, automatic response if there are signs of intrusion.
This will detect potential problems such as the “one computer in the entire network” that is talking to a computer in a country in which the company has no business, Mr. Rajewski said.
Knowing what to do if an event occurs is crucial, experts say.
Companies should have an incident response plan that includes a playbook “so everyone in the organization, from the most senior executive to the summer intern, understands what they need to do if a ransomware event occurs,” Mr. Finan said.
Tabletop exercises should be performed at least quarterly to test incident response plans and update them as needed, experts say.
Robust backup solutions should also be in place to allow companies to get back up and running if they are hit by a ransomware attack, said Jason Rebholz, Alexandria, Virginia-based chief information officer at insurtech Corvus Insurance Holdings Inc.
It is critically important the backup is “super isolated, actually viable” and tested regularly, Mr. Rajewski said.
Experts say companies should have a “3-2-1” backup strategy, which refers to having three copies of data on two different media and one copy off-site, which could include one that is cloud-based.
One data storage approach for backups is “write once, read many,” or WORM, which prevents the data from being overwritten or modified and protects against hackers. “It’s there forever,” said Raf Sanchez, London-based global head of cyber services for Beazley PLC.
Basic security protocols sufficient to deter many hackers
Although companies may always find themselves to some extent playing catch up with cybercriminals, following basic cyber hygiene practices will go a long way toward discouraging them, experts say.
“There’s always going to be that cat-and-mouse situation, where the attackers are consistently looking for a way to bypass defenses,” said Jason Rebholz, Alexandria, Virginia-based chief information officer for insurtech Corvus Insurance Holdings Inc. “It’s not a fair fight,” he said.
“They’re very organized,” with chat rooms and websites where hackers communicate and share tools and ideas, said Shawn Melito, chief revenue officer of BreachQuest in Altoona, Pennsylvania.
Making it more difficult for hackers makes companies safer, experts say.
“There’s a misconception that these are criminal masterminds,” said Raj Samani, London-based chief scientist and fellow at cybersecurity company Trellix.
While some criminal groups are “very, very good,” others focus on well-known techniques to break into companies and “it’s not impossible to stop them,” he said.
“Cybercriminals are like water,” said Tom Finan, director, cyber practice, for Willis Towers Watson PLC in Washington. “They are going to find the least path of resistance to get where they are going to go. … There’s a lot more work organizations can do” to discourage them.