Global data security threats evolve as hackers hold businesses to ransom
Companies face choice of paying up or losing often-sensitive information Reprints
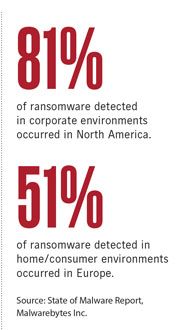
Virtual shakedowns of organizations via ransomware computer software are becoming both more prevalent and more sophisticated, and are an increasingly major problem for businesses.
Although primary targets are small and midsize businesses and health care institutions, all companies are vulnerable to ransomware, which involves criminals encrypting data and preventing companies’ access to their files without first paying a ransom — generally in bitcoin, the untraceable digital currency.
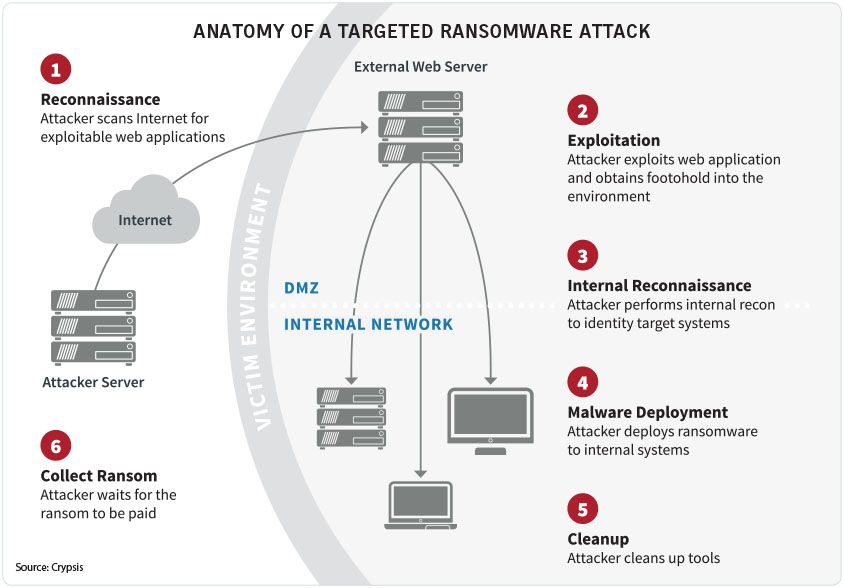
The infected software is often downloaded through “phishing,” when employees inadvertently click on phony links.
Observers say major factors behind its prevalence is that criminals generally demand relatively small amounts, often only a few thousand dollars, which makes it worthwhile for businesses to accede to their demands — although there is no guarantee their data will be restored uncorrupted, if at all, or that the criminals won’t return for another bite of the apple.
There are steps companies can take to avoid falling victim to ransomware, most notably employee training, and insurance coverage is readily available.
Ransomware “is increasing, and it’s increasing on a global scale,” said Alan Brill, senior managing director at Kroll Associates Inc. in Secaucus, New Jersey.
Ransomware incidents among Beazley P.L.C. clients, for instance, more than quadrupled in 2016 over 2015’s total to more than 200 and are expected to double in 2017, according to a report issued by the insurer in January. And there isn’t any end in sight, as defenders struggle to stay one step ahead of criminals.
Reports of ransomware so far this year include a police department in Cockrell Hill, Texas, that lost eight years’ worth of data because of a ransomware attack, and a four-star resort hotel in Austria that paid about $1,600 in ransomware after hackers penetrated its security system and locked its room doors from the inside.
“Basically, the criminals figured out it’s a lot easier to deny access to information rather than trying to implant malware, exfiltrate data and sell it on the web,” said John Riggi, Washington-based managing director in BDO Consulting’s technology advisory services practice and head of its cyber security and financial crimes unit. “It’s been a pretty effective business model.”
The small amount the criminals demand “sometimes makes it easy for a company to want to pay,” said Dave Navetta, a partner with law firm Norton Rose Fulbright US L.L.P. in Denver.
However, he warned, there is no guarantee that the amounts being demanded will not increase.
“The frequency is there. What hasn’t happened yet is the severity,” said Ben Beeson, Washington-based vice president for cyber security and privacy at Lockton Cos. L.L.C.
Meanwhile, the ransomware itself is becoming more sophisticated as it evolves, experts say. “It’s being updated faster and faster, so it becomes more difficult to recognize it” when it infects systems, Mr. Brill said.
In addition, new versions of ransomware copy whatever they encrypt, so “now the threat is, if you don’t pay the money, not only will you not have access to (the data) but ‘I’m going to release it to the world,’” Mr. Brill said.
“Ransomware is becoming smarter,” said Mr. Navetta. Rather than encrypting only the data it first touches, he said, it can now look for certain types of more valuable data.
Sixty new types of ransomware were distributed last year, said Bill Hardin, Chicago-based vice president at consulting firm Charles River Associates. “They’re always one step ahead.” Companies of all sizes are at risk, say experts.
Ransomware is “a largely automated business, so they’re sending out tons of phishing emails. And since it costs them essentially nothing, they’re going on the fact that some small percentage of people will fall for it,” said Mr. Brill. The criminals have even established call centers that direct victims how to pay in bitcoin, he said.
Health care, however, remains a particular target, as well as school districts, higher education and government agencies — all of which may have less robust cyber security systems than large corporations, experts say.
Just by the nature of it being health care, the sector has “more significant exposures. It truly could be a life-or-death situation,” said Erica Davis, New York-based head of specialty products errors and omissions at Zurich North America.
Read Next
-

Keep staff, technology updated to reduce malware vulnerability
A critical factor in avoiding ransomware attacks is training employees to be exceedingly cautious about clicking on email links.