Final cyber rule eases insurer concerns
Posted On: Mar. 6, 2017 12:00 AM CSTNew York’s final cyber security rule for insurers and other financial institutions is much less prescriptive than the original proposal, but it is still raising compliance concerns.
The final rule, which became effective March 1, requires companies to put in place controls to ensure a robust cyber security program, including requirements for a program that is adequately funded and staffed, overseen by qualified management and reported on periodically to the board or the most senior governing body of the organization.
The New York State Department of Financial Services received more than 150 comments during two public comment periods after the release of the initial proposal in September 2016, and amended the final regulation in several critical ways, experts say.
“They paid attention to many of those comments,” said Theodore Augustinos, a Hartford, Connecticut-based partner with Locke Lord L.L.P. “While the cyber security regulation still imposes very onerous requirements on anyone who is licensed with the New York DFS, the changes were very sensible.”
The key change, experts agreed, was that although the original proposal featured a series of rigid requirements, the final rule evolved into a more flexible approach that allows companies to develop a cyber security program based on their individual risk assessments, with most of the requirements now tied to those risk assessments.
“In looking back at the initial regulation that was proposed, I think our biggest concern was that it was far too prescriptive, it was too detailed and didn’t allow companies to utilize a risk-based approach to cyber security,” said Alison Cooper, Albany, New York-based Northeast region vice president of state affairs for the American Insurance Association. “Some of those initial requirements were so restrictive, we actually worried that there would be an unintended consequence of reducing security rather than enhancing it.”
The final version still presents compliance challenges but “it gives great flexibility for insurers to tailor their cyber security programs in a risk-based manner,” she said.
However, the department also stated that while it believes that each organization should model its cyber security program on its individual cyber security risks, the risk assessments are not intended to be a cost-benefit analysis of cyber security.
“They’re saying ‘yes, you can have a program tailored to your specific risks, but you can’t say that the cost of compliance is a burden as compared to the benefit,’” said Andrew Holland, leader of the insurance regulatory practice at Sidley Austin L.L.P. based in New York. “They’ve definitely given something there, but they’ve also set a high bar.”
In addition, unlike the original proposal, the final rule does not mandate that financial institutions always use encryption. Instead, they can use alternative controls reviewed and approved by their chief information security officer. Mr. Holland called this revision a “big practical change” that recognizes that encryption may not be feasible in some circumstances, particularly for entities with older legacy systems.
The original proposal would have also required financial institutions to notify the department of both successful and unsuccessful cyber attacks, but the final rule evolved to require notification only of attempts that have a reasonable likelihood of causing material harm to the firm’s business operations.
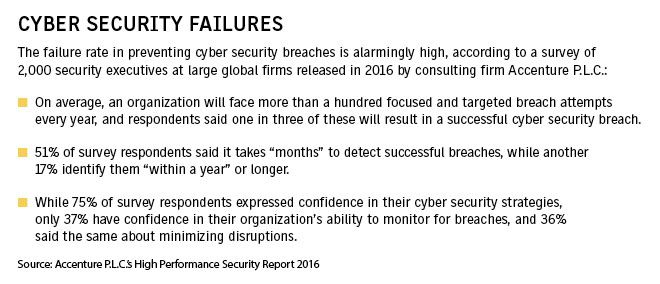
Financial institutions are frequently targeted by cyber criminals but most attacks are repelled by the security measures they have in place.
“The final rule still does reference attempted attacks, however, because of the insertion of the materiality standard and the more risk-based nature of the regulation in general. It ensures that you’re only focusing on those types of run-ofthemill instances when they might actually pose a significant problem for some reason,” said Kristina Baldwin, Albanybased vice president of state government relations for the Property Casualty Insurers Association of America.
But the department maintained some parts of the rule that had been criticized, including challenges to the scope of the regulation, which applies to all entities licensed by the department, and an “overbroad” definition of information systems to be protected. And financial institutions must take action such as hiring a chief information security officer and developing and implementing an incident response plan ahead of quickly approaching deadlines featured in the regulation, experts say.